A word of caution about the security of run-only scripts.
Please be aware that exporting a script as Run-Only only prevents others from seeing your script’s source code. It does not conceal literal data stored within your script. If you are embedding sensitive information, such as passwords, within your script’s source code then you need to find another solution.
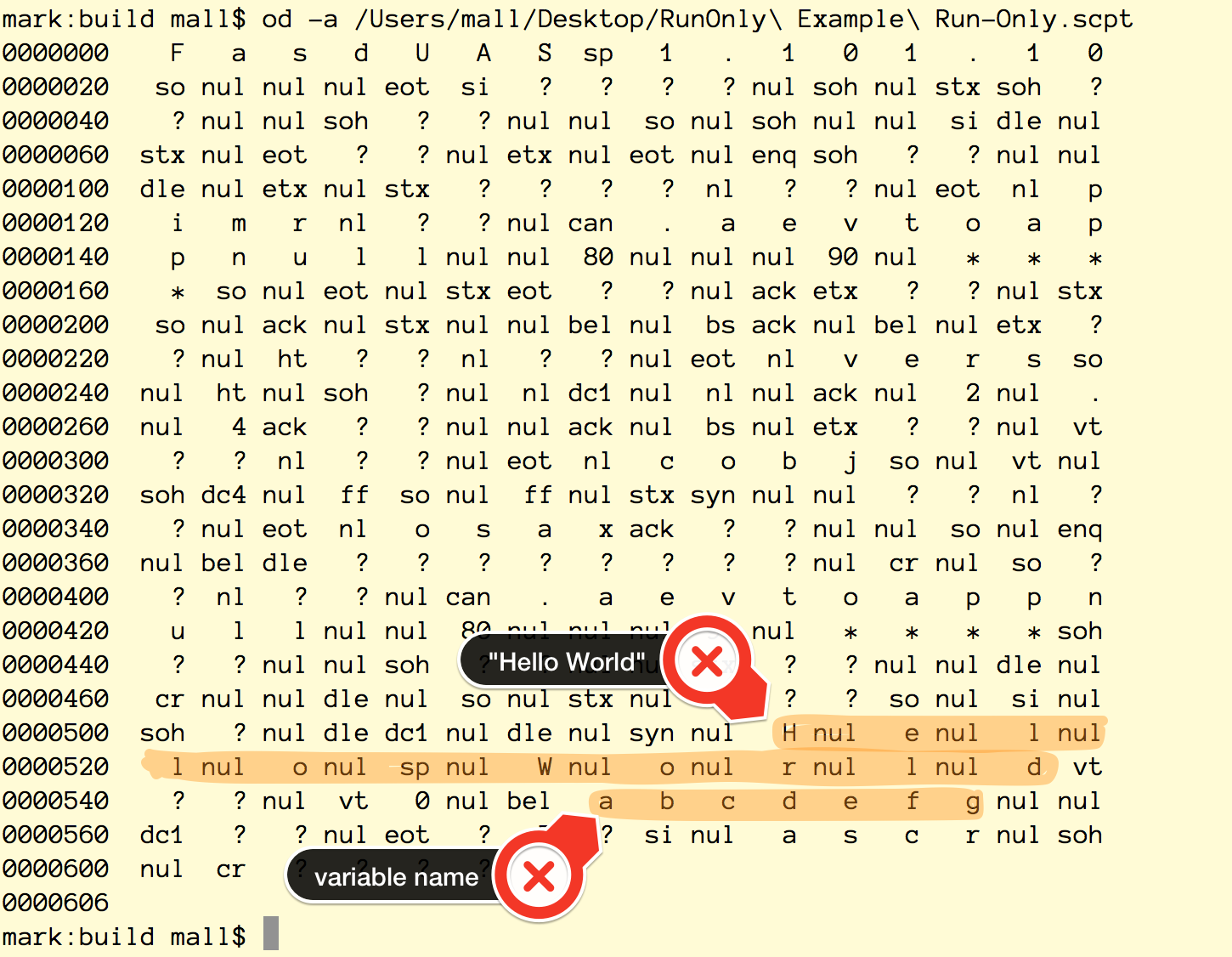
Take this example:
use AppleScript version "2.4" -- Yosemite (10.10) or later
use scripting additions
set abcdefg to "Hello World"
If you export this code as a Run-Only script, its pretty easy to recover variable names and string literals. Here’s how using the Unix od command:
Obviously, in a longer script it will be more difficult to find the string literals and variable names, but it is possible. Someone with a little determination can recover your data.
I suggest reading sensitive data from config files which are secured and don’t travel with the script. If you must embed a password or obscure URL, a less secure solution is breaking up string literals into to pieces and assemble the final string at runtime.
This is nothing new. AppleScript has operated this way since version 1.